Email marketing is a powerful way to communicate with your customers and prospects. But if you're spending hours crafting emails for each person or sending generic email blasts, you're not getting the most out of your email marketing campaigns. Email automation can free up your time and allow you to streamline your email campaigns, enabling your business to get the most out of them.
Give your business a boost by using email automation

From Big Data To Smart Data: How Manufacturers Can Drive Greater Value From Industrial Data

With manufacturing data volumes growing faster than any other industry, #dataoverload can hamper operations and decisionmaking. Here’s how AI can help:
Surface Studio 2+ | Hands-On & Overview

Reimagine the way you work with the @Microsoft Surface Studio 2+! Check out this video for a hands-on demo and close-up look at the amazing things this device can do. ? Part desktop, part tablet, the Studio 2+ folds flat for whiteboarding, creating, and more. These will sell fast, so be sure to contact Virtual Office Solutions to get yours today.
Where to Focus Your Company’s Limited Cybersecurity Budget
Targeted cybersecurity spending is essential to both protecting your organization and ensuring you don’t blow up your #ITbudget. Important analysis ?
Microsoft Surface: Business Ready for Hybrid Work
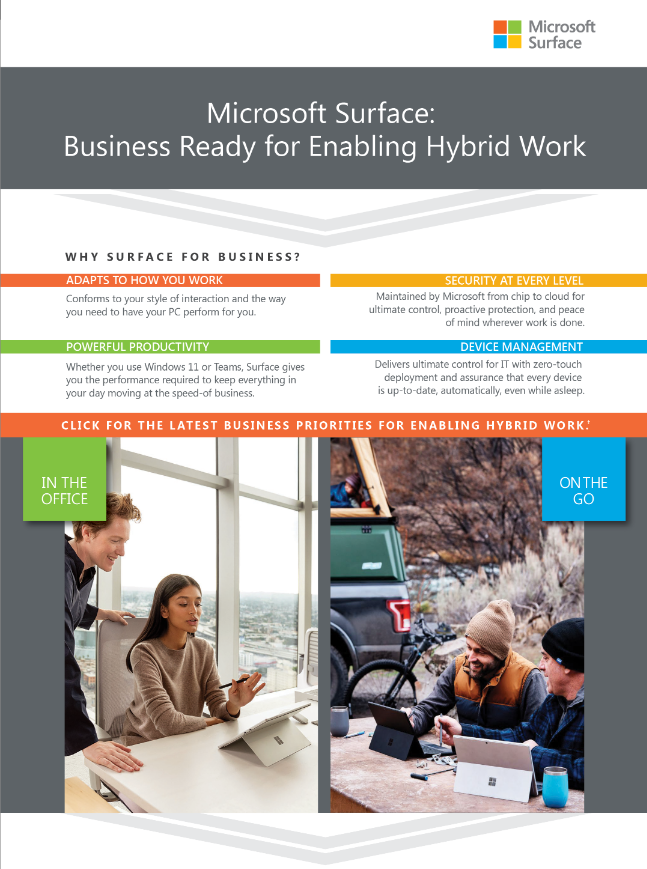
The @Microsoft Surface for Business hybrid work portfolio is here. ? Order yours NOW! Check out this graphic to learn about these devices—and be sure to click the orange bar and scroll over elements to reveal details you need to know. To place your orders, contact Virtual Office Solutions today.
Future-proof your business with IT security audits

Business owners often grapple with protecting sensitive data and maintaining the trust of their clients. Amidst the evolving threat landscape, IT security audits have emerged as a formidable tool to fortify your defenses and ensure the resilience of your operations.
IT Leads the Evolution of the Workplace
IT leads the way as the modern workplace evolves! Check out this infographic from #HP to discover how IT has become the leader as workplaces continue to evolve. ? For HP solutions that can help your workplace adapt, contact Virtual Office Solutions.
What Is ‘Responsible AI’ And Why Is Big Tech Investing Billions In It?

AI’s popularity is increasingly being tempered by its ethical implications. Important development on #EthicalAI:
A complimentary assessment of your cybersecurity strategy

Schedule a free consultation with a security expert at Virtual Office Solutions to assess whether your #cybersecuritystrategy is optimized for today’s threat landscape.